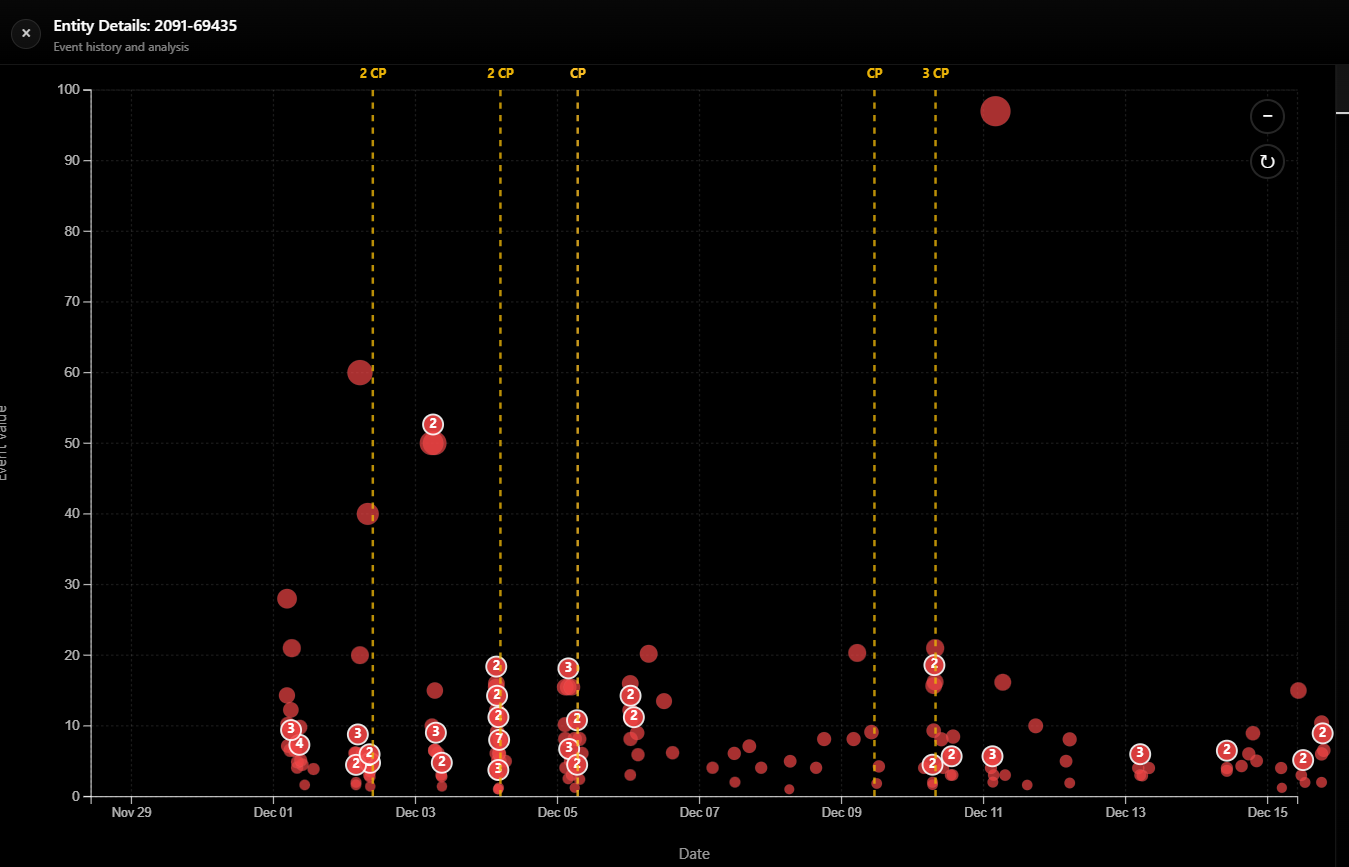
Detect Suspicious Account Networks In Money Transfer Systems
Veltrix helps remittance providers identify suspicious account networks,
unusual transaction structures, and hidden behavioral patterns across
high-volume money transfer systems.
Veltrix helps remittance providers identify suspicious account networks,
unusual transaction structures, and hidden behavioral patterns across
high-volume money transfer systems.